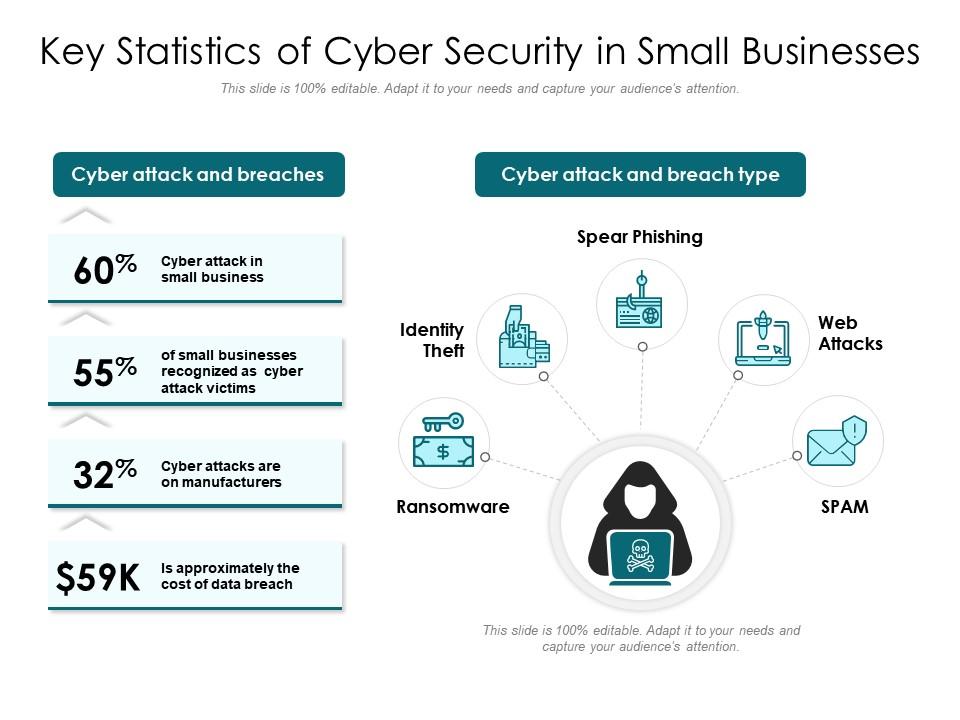
In 2023, the urgency for implementing robust security strategies for small businesses has reached a critical point. With over 43% of cyberattacks specifically targeting small businesses and projected annual losses soaring to $27 billion (SmallBizTrends), the stakes have never been higher.
However, small businesses often face budget constraints that make enterprise-grade security solutions unattainable. This article aims to bridge that gap by offering a comprehensive cybersecurity action plan tailored for small businesses. Follow these 10 essential security strategies to protect your organization’s assets, data, and future.
Conduct a Thorough Small Business Security Audit
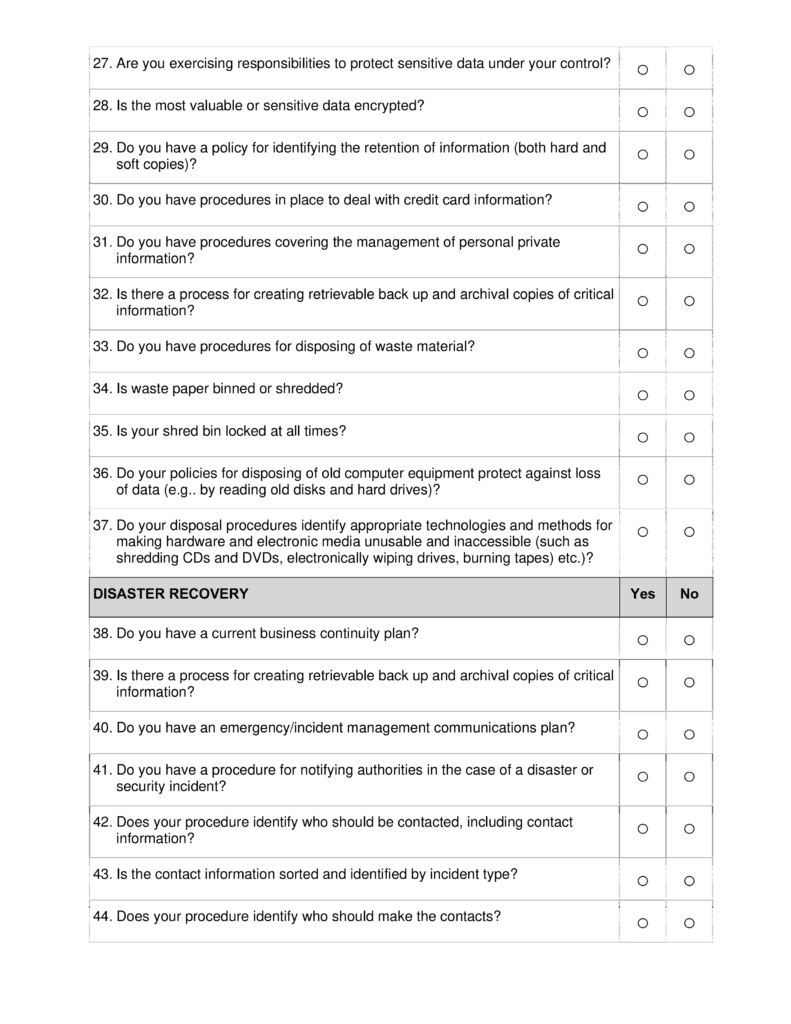
The first step in security strategies for small businesses is performing a complete audit. Document your tech stack, processes, and policies to uncover vulnerabilities.
- Conduct network scans to identify unpatched devices and outdated software in need of upgrading to avoid vulnerabilities.
- Review permissions and access controls across systems to ensure least privilege principles are in place.
- Use risk assessments like VTRA to quantify and prioritize discovered risks and exposures.
- Schedule annual audits or whenever major changes occur to stay on top of weaknesses.
Regular small business security audits provide the foundation for all other cyber strategies by mapping your risk landscape.
Make Cybersecurity Training Mandatory for Employees
Your employees are your first defense against cyber threats. But they can also be the biggest risk if not properly trained. Prioritize company-wide security awareness programs as part of your small business strategies.
- Educate staff on latest social engineering and phishing scam tactics through real-world examples. Reinforce best practices for identifying risks.
- Ensure everyone understands security policies like strong passwords, safe web use, access controls and the consequences for violations.
- Consider gamifying training via interactive modules with quizzes and rewards to boost engagement. Schedule refreshers quarterly.
Equipping staff at all levels with cybersecurity know-how will drastically improve resilience. Don’t overlook this critical human element.
Enforce Strong Passwords and Two-Factor Authentication (2FA)
Weak passwords play a role in over 80% of cyber incidents (Verizon). For sound security strategies, enforce password complexity standards across your systems.
- Require 12+ character passwords using upper/lowercase letters, numbers and symbols. Prohibit easily guessed passwords.
- Implement two-factor authentication (2FA) for enhanced protection. Users must enter a random code from their phone when logging in.
- Provide a password manager like LastPass to generate strong, unique passwords for all employees. Remove password reuse risks.
- Make 2FA mandatory for email, cloud services, VPNs, and other access points.
Robust password policies and 2FA are security fundamentals no small business should overlook.
Maintain Regular Software Updates
Cybercriminals target vulnerabilities in outdated programs. Consistently updating software is a cyber hygiene essential.
- Automate updates where possible. For other apps, designate someone to manage patching.
- Closely monitor vendor changelogs for new updates. Remove end-of-life software no longer receiving support.
- Be proactive following incidents like Log4j where patching against active exploits becomes urgent. Never ignore a software update.
Keeping systems current with the latest security fixes should be a top priority among security strategies for small business IT.
Implement Automated Backups and Recovery
Ransomware attacks can unravel small businesses without reliable backups. Automated daily data backups provide an insurance policy against cyber incidents.
- Use cloud backup services like Carbonite in addition to local external hard drive backups for maximum redundancy.
- Ensure backups are encrypted and securely stored. Test restoration periodically to verify effectiveness.
- Document detailed recovery plans for responding to incidents and restoring business operations.
Effective backup and recovery capabilities give small businesses resilience against cyber disruptions. Don’t wait until it’s too late.
Leverage Encryption to Secure Sensitive Small Business Data
Encryption converts data into coded form so only authorized parties can access it. Encrypting sensitive information is a best practice among small business security strategies.
- Encrypt data in transit via VPN, SSL/TLS and HTTPS.
- Encrypt data at rest via disk and database encryption safeguards.
- Encrypt archives, documents, emails and artifacts containing private customer, financial or strategic data.
- Enable full-disk encryption on company laptops and mobile devices to protect if lost or stolen. Manage encryption centrally.
The right encryption applied to your crown jewels can prevent devastating data compromise resulting from cyberattacks.
Monitor Networks to Detect Threats Early

Monitoring network activity provides visibility enabling early threat detection. This should be a key part of your small business security strategy.
- Implement SIEM software like AlienVault to aggregate and analyze security alerts across systems.
- Enable endpoint detection (EPD) to monitor activity on individual devices, and catch intrusions rapidly.
- Monitor VPN connections, email links and attachments and othervectors closely for signs of compromise.
Vigilance through robust monitoring can help cut response times drastically, limiting damage from incidents.
Develop an Incident Response Plan with Procedures
Despite best efforts, cyberattacks may occur. Develop and document an incident response plan so your business can recover quickly.
- Define procedures for containment, eradication and recovery from different potential scenarios. Establish decision authority for declaring incidents.
- Maintain updated emergency contacts for your response team including technical/legal/PR personnel and executives.
- Outline communications plans for notifying affected customers, partners and stakeholders as warranted.
Having a tested plan makes navigating the chaos of an actual breach much easier. It’s a critical component of security strategies.
Schedule Ongoing Security Evaluations
Cyber threats evolve constantly, making ongoing assessments essential to evaluate effectiveness of your small business security strategies.
- Conduct quarterly vulnerability scans, penetration tests and risk analysis to identify new gaps.
- Hire third-party security firms annually for unbiased assessments. Remediate issues they uncover.
- Evaluate systems against latest frameworks like the CIS Controls or NIST CSF.
Staying up-to-date on new risks through continuous reviews will keep your security posture aligned.
Stay Informed on Emerging Cyber Threat Trends
Keeping pace with the latest cybersecurity trends helps secure your small business now and in the future.
- Read industry newsletters, blogs and alerts with actionable threat intelligence. Follow thought leaders on social media.
- Attend webinars and virtual cybersecurity conferences to discover new techniques.
- Participate in peer discussion groups like those offered by InfraGard and the National Cybersecurity Alliance.
Ongoing education ensures your strategies evolve based on the ever-changing threat landscape. Don’t get left behind.
Conclusion
Implementing tailored security strategies for small businesses is mission-critical in 2023 given surging cyber risks. Following the steps outlined in this guide will help protect your organization.
Take proactive measures from audits and backups to encryption and incident response planning using the limited budget and resources of a small business. Lock down vulnerabilities before they are exploited by attackers.
Providing cybersecurity does not need to be prohibitively expensive if the right strategic approach is pursued. With diligent execution of these 10 key security strategies for small businesses, you can help identify and mitigate risks – keeping disruptive and costly data breaches at bay.
Call to Action
Be proactive about your small business cybersecurity. Get started today by downloading our free security checklist to receive a customized audit and risk assessment. Protect your livelihood with a tailored cybersecurity strategy.


